Vulnerability Exposure & Attack Surface Management Services
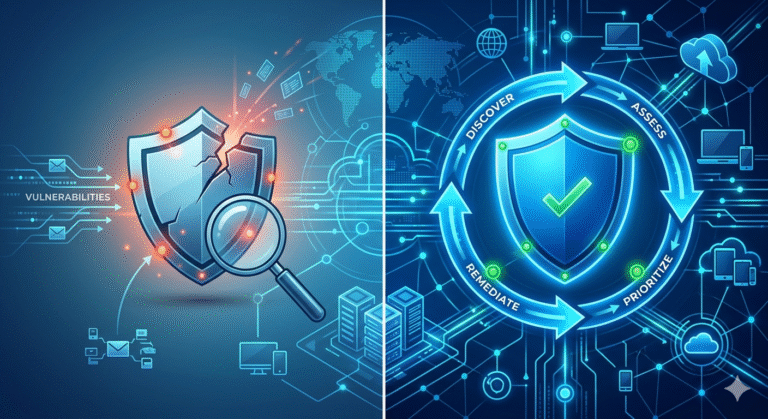
Reduce your attack surface and strengthen your security posture with Innovez Cyber’s expert-led Vulnerability Exposure and Attack Surface Management Services.
Identify, prioritize, and remediate vulnerabilities before attackers exploit them—and protect your organization proactively.
Overview
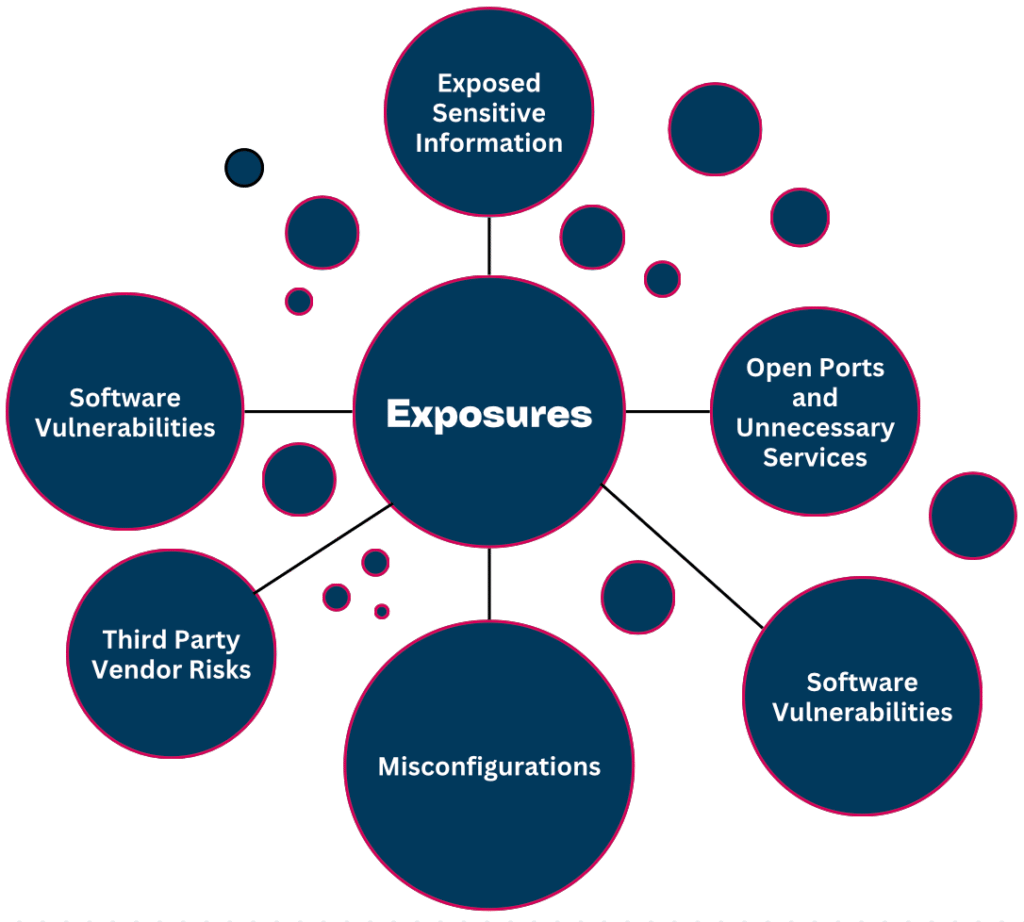
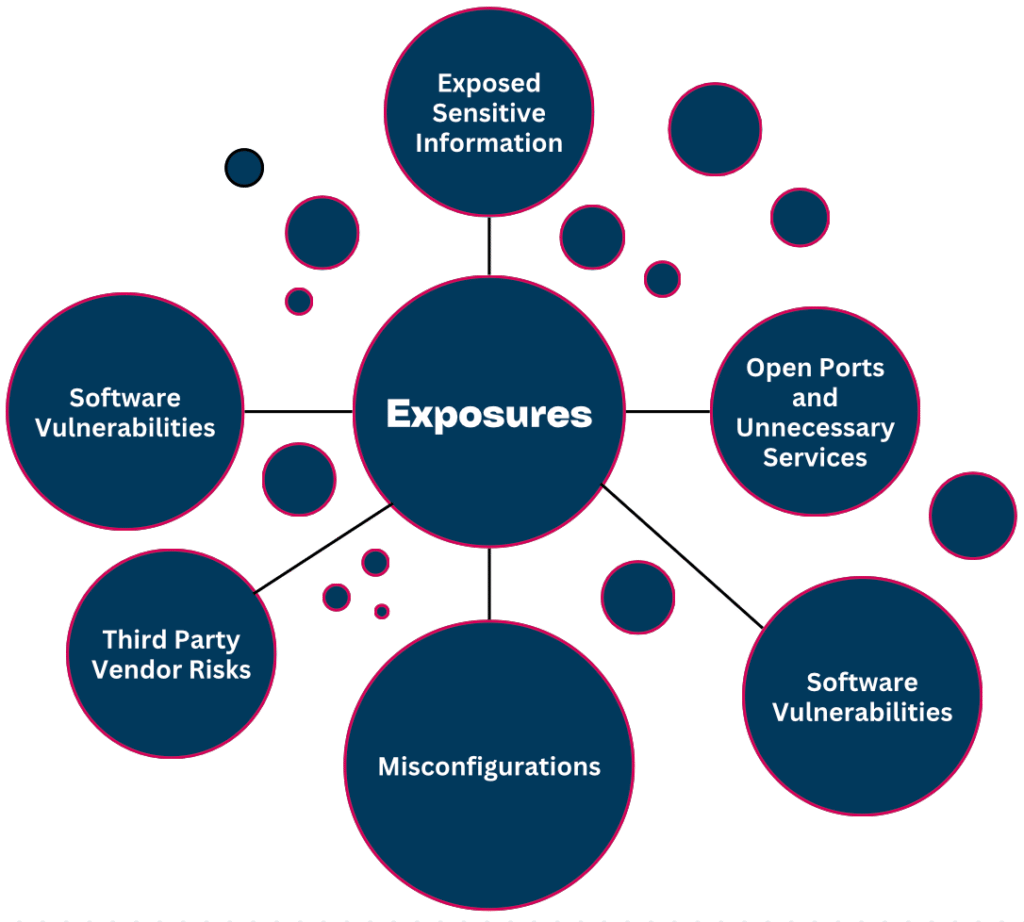
As organizations expand across cloud platforms, remote work environments, SaaS applications, and hybrid infrastructure, their external and internal attack surface continues to grow. Every exposed system, unpatched vulnerability, misconfiguration, or unmanaged asset represents a potential entry point for attackers.
Traditional vulnerability management approaches that rely solely on periodic scanning are no longer sufficient to address modern, dynamic threat environments.
Innovez Cyber provides comprehensive Vulnerability Exposure and Attack Surface Management Services designed to help organizations continuously identify, assess, prioritize, and reduce security exposures across their entire digital environment.
Our services focus on continuous exposure discovery, vulnerability risk assessment, expert analysis, remediation guidance, and ongoing monitoringensuring organizations can proactively reduce their attack surface and strengthen their overall security posture.
Our Approach: Continuous Exposure Visibility and Risk Reduction
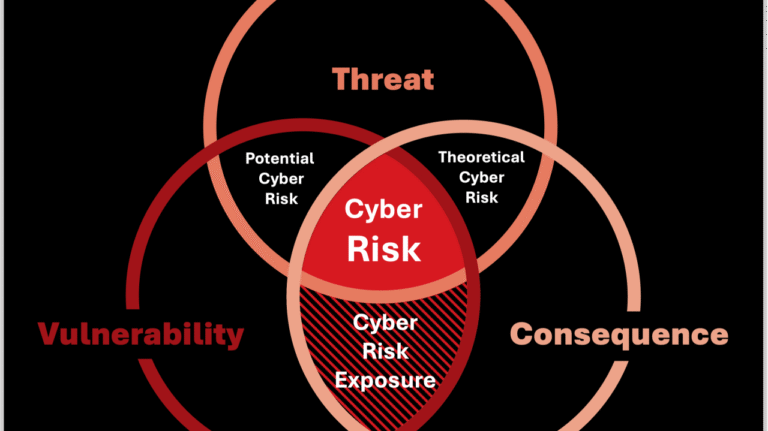
Innovez Cyber follows a risk-based exposure management approach focused on identifying real-world exploitable risks, not just theoretical vulnerabilities.
Our services emphasize:
- Continuous identification of exposed systems and assets
- Vulnerability assessment and risk analysis
- Identification of high-risk security exposures
- Expert-led vulnerability validation and prioritization
- Remediation guidance and risk reduction support
- Continuous monitoring and security posture improvement
We help organizations focus on the vulnerabilities that matter most and reduce the likelihood of successful cyberattacks.
Core Vulnerability Exposure Management Services
Vulnerability Assessment and Risk Identification
Innovez Cyber performs comprehensive vulnerability assessments across infrastructure, applications, cloud environments, and systems to identify security weaknesses.
Our services include:
- Identification of vulnerabilities across servers, systems, and infrastructure
- Detection of outdated software and insecure configurations
- Identification of missing security updates and patch gaps
- Assessment of exposed services and open access points
- Risk analysis based on vulnerability severity and exposure level
- Prioritized remediation recommendations
This helps organizations understand and address their vulnerability risks effectively.

Attack Surface Discovery and Exposure Identification
Innovez Cyber helps organizations identify and understand their complete attack surface, including both known and unknown exposed assets.
Our services include:
- Discovery of exposed internet-facing systems and services
- Identification of unmanaged or unknown assets
- Detection of exposed applications and access points
- Identification of insecure system configurations
- Assessment of cloud and external exposure risks
- Continuous monitoring of attack surface changes
This ensures organizations maintain visibility into all exposed assets.

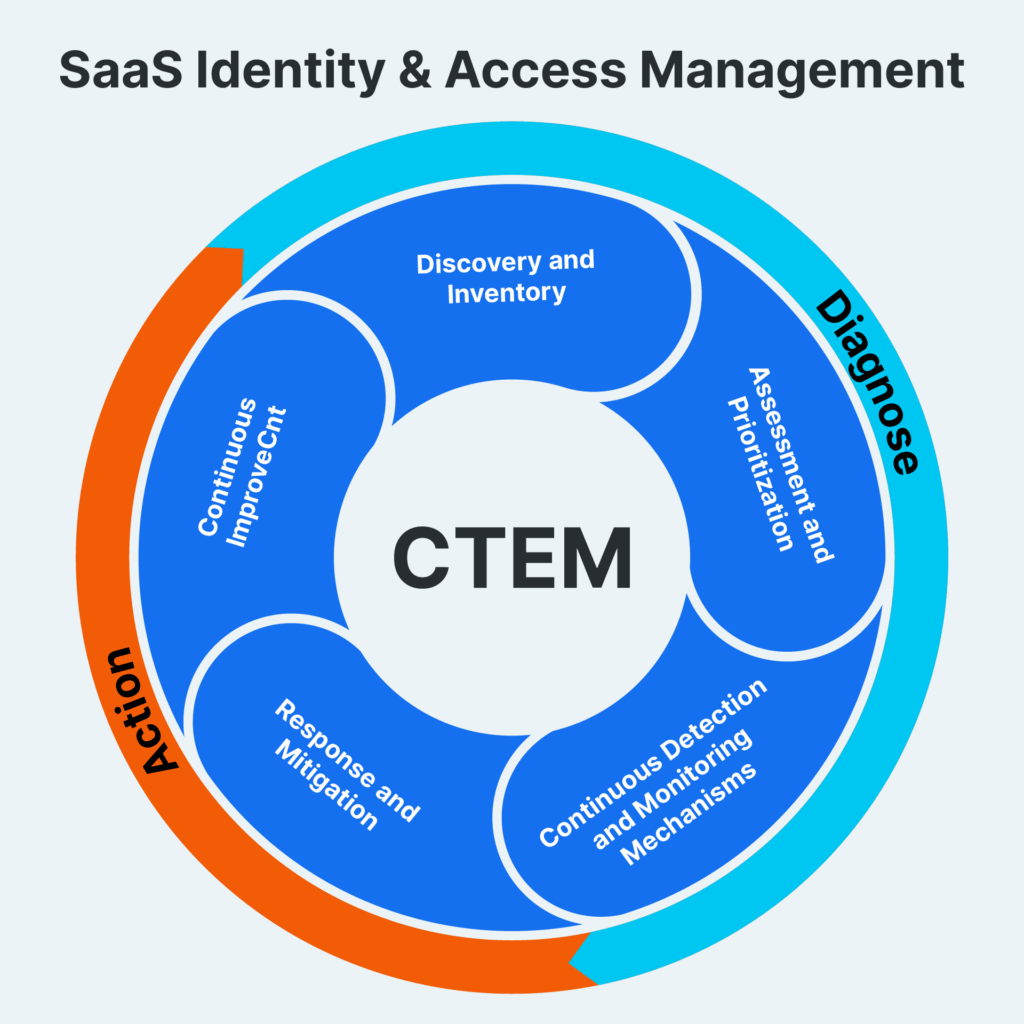
Continuous Exposure Monitoring and Risk Tracking
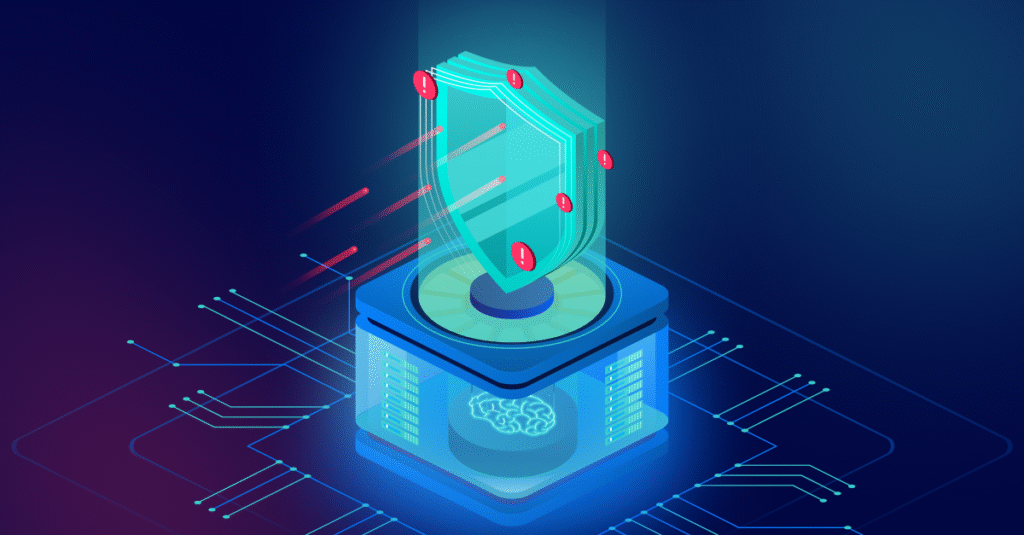
Security exposures evolve constantly as systems change, new vulnerabilities emerge, and infrastructure expands. Innovez Cyber provides continuous monitoring to detect and track new risks.
Our services include:
- Continuous monitoring of vulnerabilities and exposures
- Identification of newly introduced vulnerabilities
- Monitoring of changes in system exposure
- Risk tracking and remediation progress monitoring
- Continuous risk visibility and reporting
This helps organizations maintain an up-to-date understanding of their security exposure.

Vulnerability Risk Prioritization and Remediation Advisory
Not all vulnerabilities represent equal risk. Innovez Cyber provides expert analysis and prioritization to help organizations focus on the most critical risks.
Our services include:
- Risk-based vulnerability prioritization
- Identification of exploitable and high-impact vulnerabilities
- Remediation planning and advisory support
- Recommendations for risk mitigation and exposure reduction
- Continuous remediation guidance and tracking
This ensures efficient and effective risk reduction.

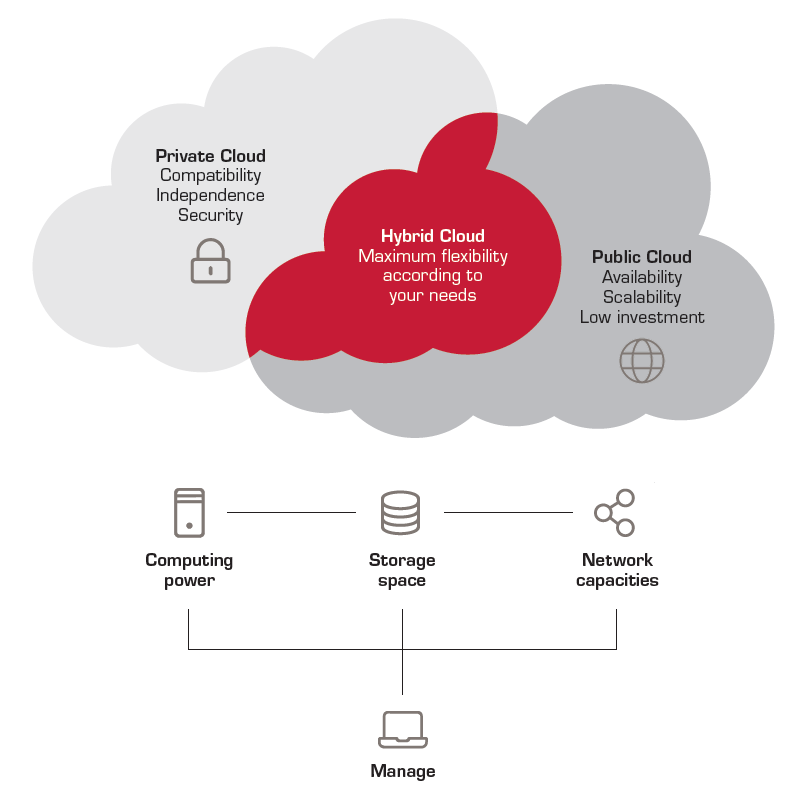
Cloud and Hybrid Environment Exposure Management
Innovez Cyber provides vulnerability and exposure management services across cloud, hybrid, and on-premises environments.
Our services include:
- Identification of cloud infrastructure vulnerabilities
- Detection of insecure cloud configurations and exposures
- Assessment of exposed cloud workloads and services
- Monitoring of cloud attack surface and risks
- Continuous exposure visibility across hybrid environments
This ensures comprehensive protection across modern infrastructure.
Application and System Exposure Assessment
Applications and systems often introduce vulnerabilities that can be exploited by attackers. Innovez Cyber provides exposure assessment services across applications and system environments.
Our services include:
- Identification of exposed applications and services
- Detection of insecure configurations and weaknesses
- Assessment of access points and system exposure
- Identification of application-related exposure risks
- Remediation advisory support
This helps protect business-critical systems from exploitation.

Exposure Investigation and Incident Support
Innovez Cyber provides expert investigation and advisory support when vulnerabilities or exposures are actively exploited or suspected.
Our services include:
- Investigation of exploitation attempts
- Analysis of vulnerable systems and exposure impact
- Incident response support and remediation guidance
- Root cause analysis and prevention recommendations
- Continuous improvement advisory
This helps organizations respond quickly and prevent future exploitation.
Key Benefits
Complete Visibility into Security Exposures
Gain full visibility into vulnerabilities and exposed systems.
Reduced Risk of Exploitation and Breach
Proactively identify and remediate vulnerabilities before attackers exploit them.
Continuous Attack Surface Monitoring
Maintain awareness of changing infrastructure and exposures.
Expert-Led Risk Prioritization and Remediation Support
Focus on the vulnerabilities that present the highest risk.
Stronger Security Posture and Reduced Attack Surface
Continuously reduce security exposures and improve resilience.
Support for Secure Cloud and Hybrid Infrastructure
Ensure consistent exposure management across all environments.
What Innovez Cyber Protects
Our services help secure:

Cloud and hybrid infrastructure
Internet-facing systems and services

Servers, endpoints, and enterprise systems

Applications and business-critical platforms

Cloud workloads and services

External and internal infrastructure
Why Innovez Cyber Vulnerability Exposure Management Services
Innovez Cyber provides modern, service-driven vulnerability and exposure management aligned with evolving enterprise environments.
Our differentiators include:
- Continuous vulnerability and attack surface monitoring services
- Expert-led exposure analysis and risk prioritization
- Cloud, hybrid, and enterprise infrastructure expertise
- Remediation advisory and risk reduction support
- Continuous monitoring and posture improvement services
- Vendor-neutral and service-centric approach
Ideal for Organizations That Require
- Continuous vulnerability monitoring and management
- Attack surface discovery and exposure visibility
- Risk-based vulnerability prioritization
- Cloud and hybrid environment exposure management
- Security posture improvement and risk reduction
- Expert advisory and remediation support
Threats We Help Prevent
Key Benefits
Innovez Cyber helps organizations reduce the risk of:
- Exploitation of known vulnerabilities
- Unauthorized access through exposed systems
- Data breaches caused by unpatched vulnerabilities
- Infrastructure compromise through exposed services
- Cloud infrastructure exploitation
- Attackers exploiting unknown or unmanaged assets
Our services help protect:
- Sensitive business and enterprise data
- Customer and personal information
- Cloud and SaaS stored data
- Financial and confidential business information
- Internal corporate and operational data
- Intellectual property and proprietary data
Our USP

AI-Native 24/7 SOC
AI embedded across detection, response & automation

Outcome-Driven Security
Focused on risk reduction, not just alerts

Continuous Validation
Always tested. Always improving security posture
Cloud & Zero Trust Native
Built for modern cloud-first enterprises
Rapid Deployment
Operational security in weeks, not months
Vendor-Neutral Approach
Unbiased, business-aligned security architecture
Common Queries You might have
Vulnerability Exposure Management is the continuous process of identifying, assessing, prioritizing, and remediating security vulnerabilities across an organization’s infrastructure, systems, applications, and cloud environments to reduce the risk of cyberattacks.
Attack Surface Management (ASM) focuses on discovering, monitoring, and securing all internet-facing and internal assets that attackers could potentially exploit.
This includes:
Exposed servers and systems
Cloud services
Applications and APIs
Remote access infrastructure
Unknown or unmanaged assets
Organizations often have more exposed assets than they realize. Without proper visibility, attackers may find vulnerable systems before security teams do.
Attack surface visibility helps organizations:
Identify unknown assets
Detect exposed services
Reduce entry points for attackers
Improve overall security posture
Our assessments detect a wide range of vulnerabilities including those listed in the Common Vulnerabilities and Exposures (CVE) database and common weaknesses such as:
Missing security patches
Insecure system configurations
Outdated software
Exposed services and ports
Authentication and access control weaknesses