Security. Transparency. Trust. Built In.
At Innovez Cyber, trust is not claimed — it is engineered into everything we do.
We secure your data, systems, and operations with enterprise-grade practices, responsible AI, and transparent governance.
Driven by Innovation. Powered by Integrity.
Engineering Trust. Securing the Future.
OUR TRUST FRAMEWORK
Security by Design
Built on Zero Trust and secure-first architecture
Responsible AI
Ethical AI aligned with ISO 42001 principles
Transparency
Clear, honest, and accountable data practices
Enterprise Governance
Enterprise Governance
Continuous Monitoring
Real-time detection, response, and visibility
SECURITY PRACTICES

How We Secure Your Environment
We implement enterprise-grade security controls to protect your data and operations:
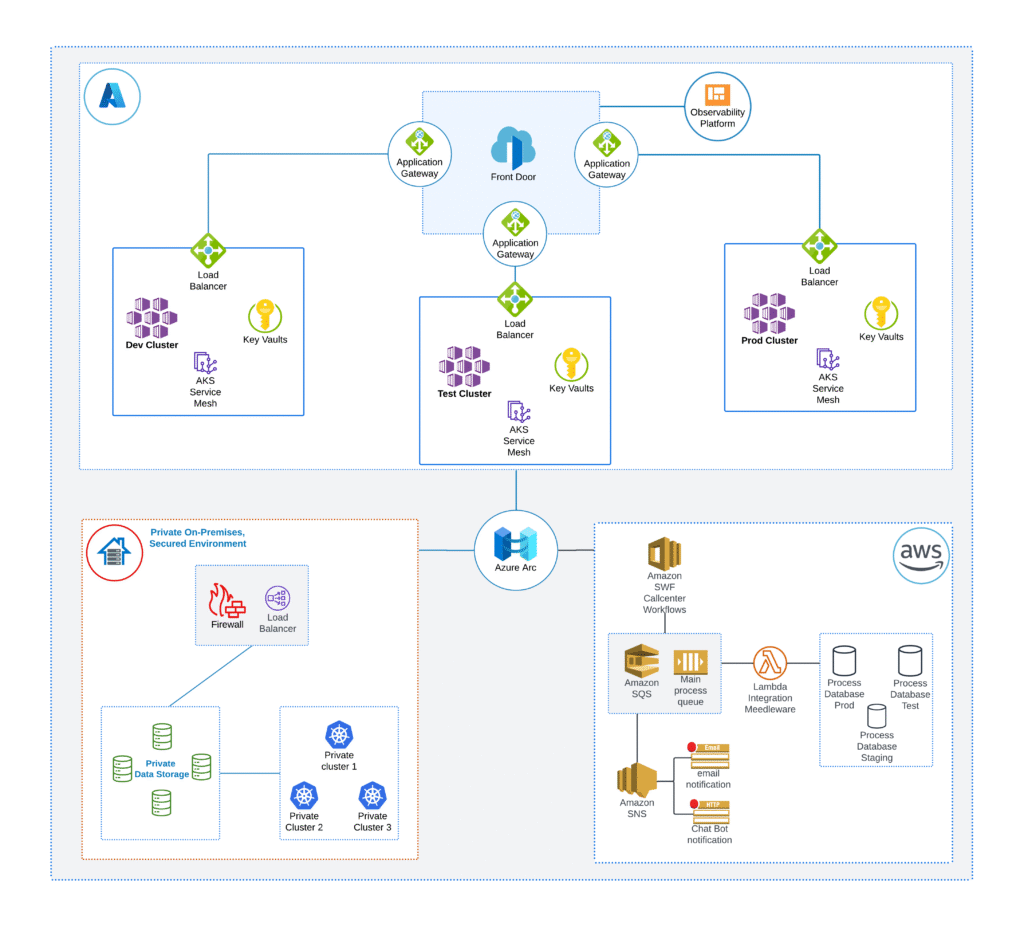
- Zero Trust Architecture
- Role-Based Access Control (RBAC)
- Encryption (data in transit & at rest)
- Continuous monitoring and threat detection
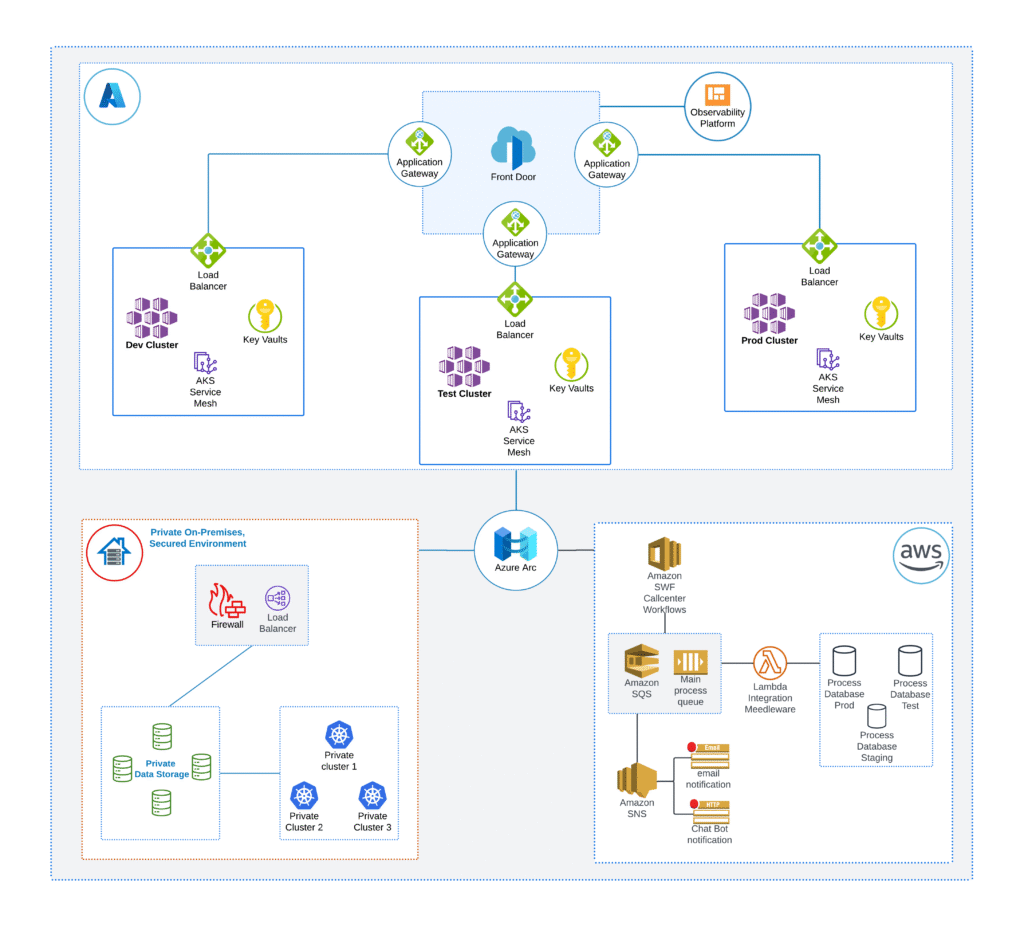
- Secure cloud configurations (Azure / AWS / GCP)
👉 Your environment is continuously protected, monitored, and controlled.
AI GOVERNANCE & RESPONSIBLE USE
We use AI to enhance cybersecurity — responsibly and transparently.
- AI supports threat detection and automation only
- All critical decisions involve human oversight
- No unauthorized profiling or automated risk decisions
- Client data is never used for AI training without explicit consent
Aligned with ISO/IEC 42001 (AI Management Systems)
CLIENT DATA PROTECTION (ENTERPRISE FOCUS)
Your Data, Your Control
- Clients retain full ownership of their data
- We act as a data processor (where applicable)
- Access is restricted using least privilege principles
- Data is processed only for defined security purposes
👉 We follow a strict no data-selling, no misuse policy.

COMPLIANCE & STANDARDS
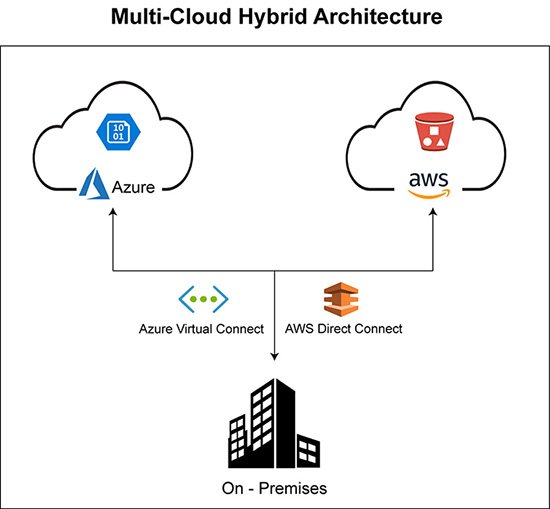
We align with globally recognized frameworks:
- ISO 27001 – Information Security
- ISO/IEC 42001 – AI Governance
- NIST Cybersecurity Framework
- GDPR (where applicable)
- India DPDP Act

DATA LIFECYCLE MANAGEMENT
How We Handle Data
- Collect → Minimal and purpose-driven
- Process → Only for defined security use
- Protect → Encryption and strict access control
- Monitor → Continuous visibility and logging
- Delete → Secure disposal when no longer required
INCIDENT RESPONSE & BREACH MANAGEMENT
Prepared for What Matters Most
- 24×7 monitoring and alerting
- Rapid incident detection and response
- Structured escalation workflows
- Client notification within 24–72 hours (as applicable)
- Root cause analysis and remediation

THIRD-PARTY & SUB-PROCESSOR MANAGEMENT
- Only trusted and vetted partners are used
- All partners are contractually bound to security standards
- Security and compliance due diligence is performed
- Sub-processor details available upon request
Key Benefits
Improved Application Security Posture
Identify and remediate vulnerabilities before attackers exploit them.
Secure Application Development and Deployment
Integrate security across development and deployment processes.
Protection Against Application and API Attacks
Detect and respond to application-based threats quickly.
Expert Security Guidance for Development Teams
Strengthen development security without slowing innovation.
Continuous Monitoring and Risk Visibility
Maintain visibility into application and API security risks.
Reduced Risk of Data Breaches
Protect sensitive business and customer data.
GLOBAL DATA PROTECTION
- Secure handling across regions and cloud environments
- Controlled cross-border data transfers
- Compliance with applicable global data protection regulations
CONTINUOUS INNOVATION
Building the Future of Cybersecurity
Innovez Cyber is continuously evolving.
We may develop:
- Cybersecurity platforms
- AI-driven security tools
- Automation and analytics solutions
👉 All future offerings will follow:
- Privacy-first design
- Strong security architecture
- Transparent data handling practices
LEGAL & POLICY ACCESS
Transparency in Action
- Privacy Policy
- Terms & Conditions
- Data Processing Addendum (DPA)
👉 Easy access. No hidden terms.
Our USP

AI-Native 24/7 SOC
AI embedded across detection, response & automation

Outcome-Driven Security
Focused on risk reduction, not just alerts

Continuous Validation
Always tested. Always improving security posture
Cloud & Zero Trust Native
Built for modern cloud-first enterprises
Rapid Deployment
Operational security in weeks, not months
Vendor-Neutral Approach
Unbiased, business-aligned security architecture