Offensive Security & Continuous Security Validation
Strengthen your security posture with Innovez Cyber’s Offensive Security and Continuous Security Validation Services.
Identify exploitable vulnerabilities, validate security controls, and protect your organization against real-world cyber threats.

Overview
Modern cyberattacks are sophisticated, targeted, and designed to bypass traditional security controls. Attackers continuously probe organizations for vulnerabilities, misconfigurations, exposed services, and weak access controls that can be exploited to gain unauthorized access.
Traditional defensive security measures alone are not sufficient to identify real-world exploitable weaknesses. Organizations must proactively simulate attacker behavior to identify and remediate security gaps before they are exploited.
Innovez Cyber provides comprehensive Offensive Security and Continuous Security Validation Services designed to help organizations identify exploitable vulnerabilities, validate security controls, and strengthen their overall security posture.
Our expert-led services simulate real-world attack scenarios, assess infrastructure, applications, identities, and cloud environments, and provide actionable remediation guidance to reduce security risk and improve resilience.
Our Approach: Simulating Real-World Attacker Techniques
Innovez Cyber adopts a structured offensive security approach aligned with modern threat actor tactics, techniques, and procedures.
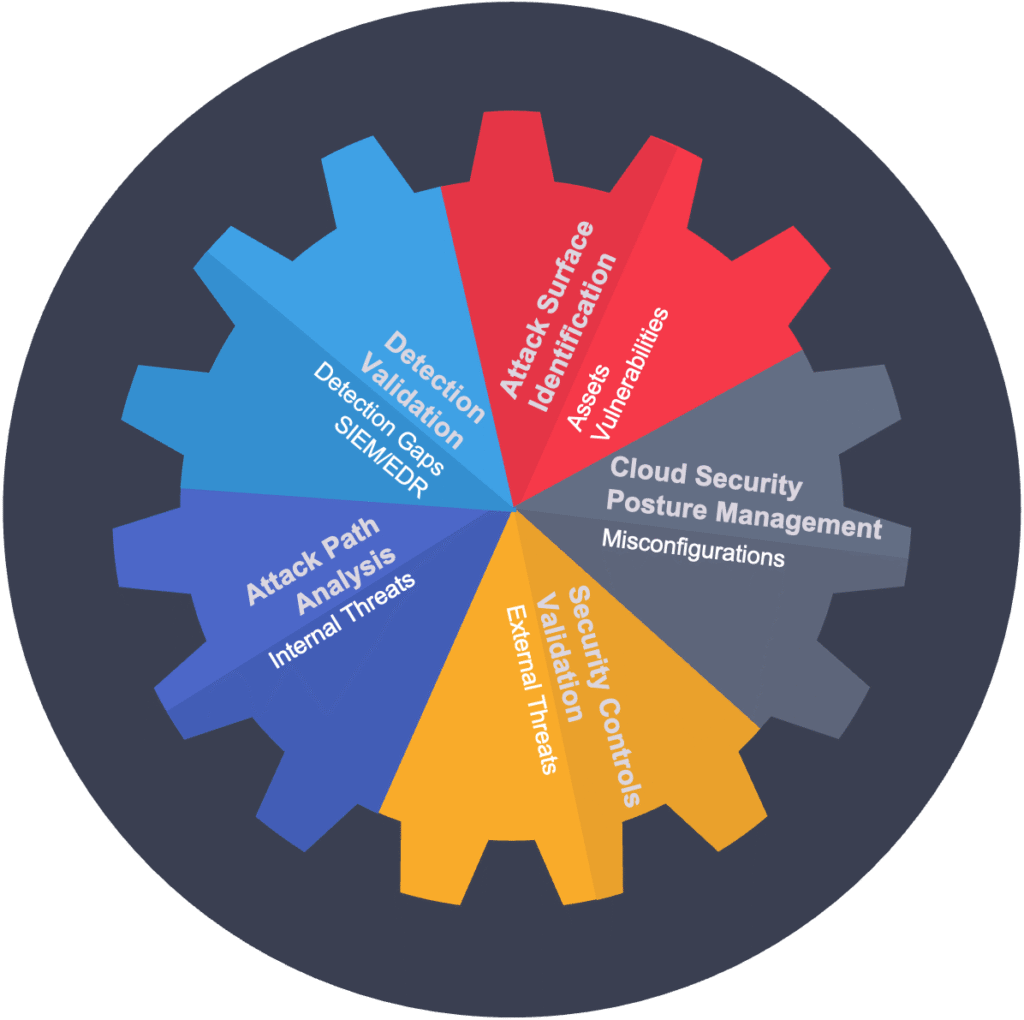
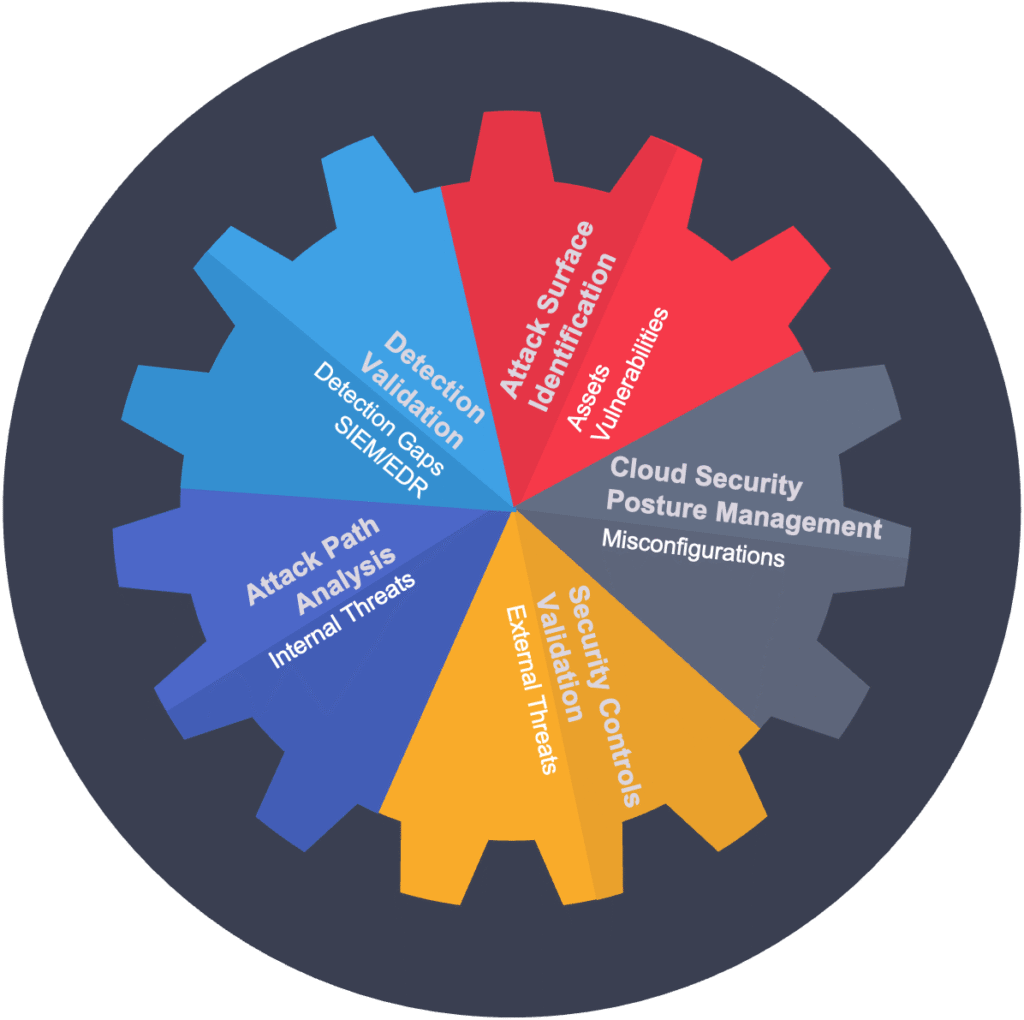
Our services focus on:
- Identifying exploitable vulnerabilities and security weaknesses
- Simulating real-world attack scenarios
- Assessing security controls and defensive effectiveness
- Validating detection and response capabilities
- Providing prioritized remediation guidance
- Supporting continuous security posture improvement
We help organizations understand how attackers view their environment and how vulnerabilities can be exploited.

Core Offensive Security Services

Penetration Testing Services
Innovez Cyber performs comprehensive penetration testing to identify vulnerabilities that attackers could exploit.
Our services include:
- Infrastructure penetration testing
- Cloud environment penetration testing
- External and internal penetration testing
- Application and API penetration testing
- Identity and access control penetration testing
- Privilege escalation and lateral movement testing
- Security control effectiveness validation
This helps organizations identify and remediate exploitable weaknesses.
Red Team Simulation Services
Innovez Cyber conducts advanced red team exercises that simulate real-world cyberattacks to evaluate the organization’s ability to detect and respond to threats.
Our services include:
- Adversary simulation aligned with modern threat techniques
- Testing of identity, infrastructure, and application security
- Simulation of attack paths and exploitation scenarios
- Evaluation of detection and response effectiveness
- Identification of security gaps and control weaknesses
- Recommendations for improving defensive capabilities
This helps organizations understand their real-world security readiness.
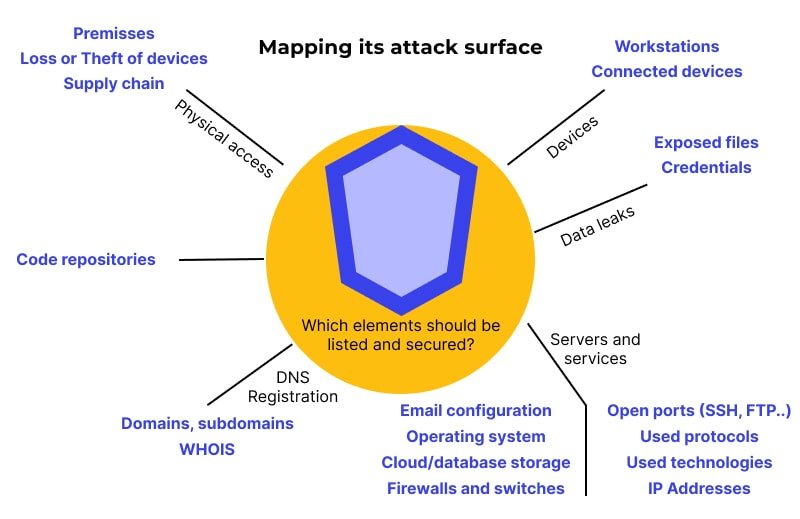
Attack Surface Exploitation and Validation
Innovez Cyber helps validate the security of exposed systems and services by simulating exploitation scenarios.
Our services include:
- Identification of exposed and vulnerable systems
- Exploitation simulation of identified vulnerabilities
- Validation of exposure risks and security impact
- Analysis of potential attack paths
- Remediation and risk mitigation advisory
This helps organizations reduce exploitable attack surface.
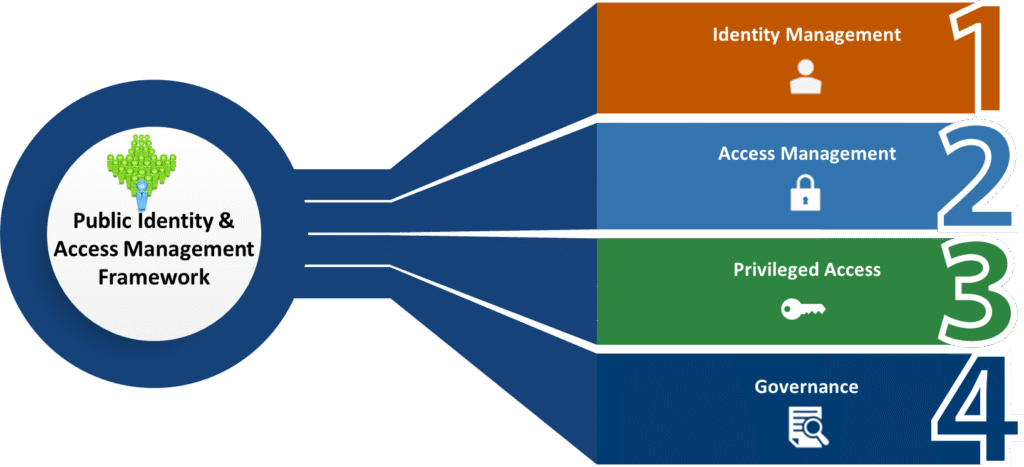
Identity and Privileged Access Security Testing
Identity compromise is one of the most common attack vectors. Innovez Cyber performs testing to identify identity-related security weaknesses.
Our services include:
- Assessment of identity and authentication security
- Privileged access exploitation simulation
- Identification of privilege escalation pathways
- Access control validation and risk assessment
- Recommendations for strengthening identity security
This helps protect critical identity systems.
Cloud and Hybrid Environment Security Testing
Innovez Cyber performs offensive security testing across cloud and hybrid environments.
Our services include:
- Cloud environment security testing
- Assessment of cloud access and privilege controls
- Identification of cloud misconfigurations and risks
- Simulation of cloud attack scenarios
- Validation of cloud security controls
This helps ensure cloud environments remain secure.
Continuous Security Validation and Security Posture Assessment
Security is not static. Innovez Cyber provides continuous validation services to ensure security controls remain effective.
Our services include:
- Continuous validation of security controls
- Assessment of security posture over time
- Identification of new vulnerabilities and exposures
- Ongoing remediation advisory and validation
- Continuous improvement recommendations
This helps organizations maintain a strong security posture.

Incident Simulation and Security Control Validation
Innovez Cyber helps organizations test their detection and response readiness through controlled simulations.
Our services include:
- Simulation of security incidents and attack scenarios
- Validation of detection and response processes
- Evaluation of incident response readiness
- Recommendations for improving response effectiveness
This helps organizations strengthen their defensive capabilities.
Continuous Security Validation and Security Posture Assessment
Security is not static. Innovez Cyber provides continuous validation services to ensure security controls remain effective.
Our services include:
- Continuous validation of security controls
- Assessment of security posture over time
- Identification of new vulnerabilities and exposures
- Ongoing remediation advisory and validation
- Continuous improvement recommendations
This helps organizations maintain a strong security posture.
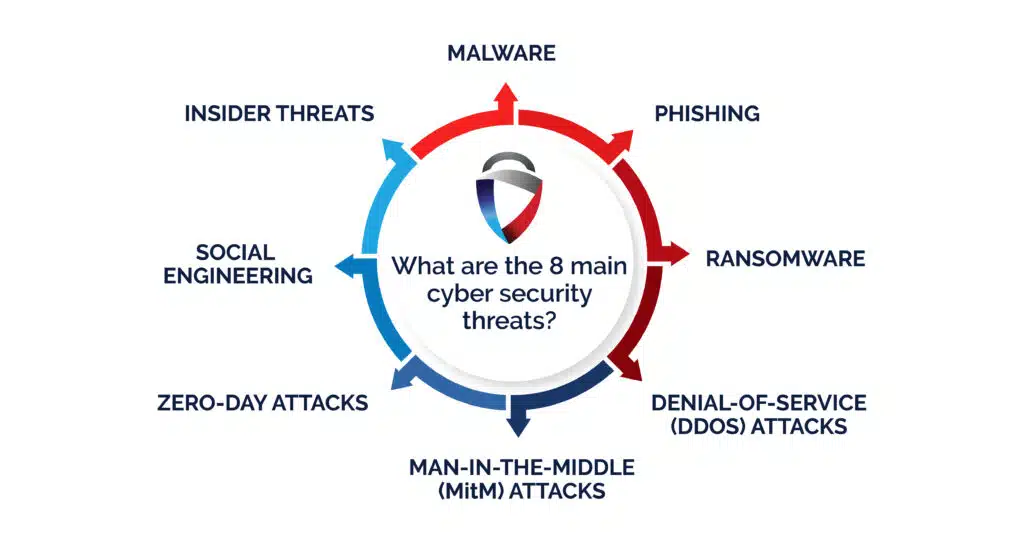
Threats and Risks We Help Identify
Innovez Cyber helps identify risks such as:
- Exploitable vulnerabilities and system weaknesses
- Unauthorized access pathways
- Privilege escalation opportunities
- Identity and access control weaknesses
- Cloud and infrastructure misconfigurations
- Exposed systems and attack surface risks
Key Benefits
Identify Real-World Exploitable Vulnerabilities
Understand actual risks that attackers could exploit.
Validate Security Control Effectiveness
Ensure security controls function as intended.
Strengthen Security Posture and Reduce Risk
Remediate vulnerabilities before attackers exploit them.
Improve Detection and Response Readiness
Enhance ability to detect and respond to attacks.
Gain Attacker Perspective on Your Environment
Understand how attackers view and target your systems.
Support Continuous Security Improvement
Maintain strong security posture over time.
Why Innovez Cyber Offensive Security Services
Innovez Cyber provides expert-led offensive security services aligned with modern enterprise and cloud environments.
Our differentiators include:
- Real-world adversary simulation expertise
- Comprehensive infrastructure, cloud, identity, and application testing
- Continuous security validation services
- Expert remediation advisory and guidance
- Service-centric and vendor-neutral approach
- Tailored testing aligned with business risk
Ideal for Organizations That Require
- Penetration testing and security validation
- Red team simulation and adversary testing
- Cloud and hybrid environment security testing
- Continuous security posture validation
- Identity and access security testing
- Proactive risk identification and remediation
Our USP
Common Queries You might have
Offensive security is a proactive cybersecurity approach that simulates real-world cyberattacks to identify vulnerabilities before attackers can exploit them. It involves testing systems, applications, networks, and cloud environments to uncover exploitable weaknesses and improve overall security posture.
Penetration testing is a controlled security assessment where cybersecurity experts attempt to exploit vulnerabilities in systems, networks, or applications. The goal is to identify weaknesses that attackers could use and provide recommendations to fix them.
Vulnerability scanning automatically identifies known security weaknesses using scanning tools, while penetration testing goes further by actively attempting to exploit those vulnerabilities to understand real-world risk and impact.
Offensive security assessments can include testing of:
Corporate networks and infrastructure
Cloud environments
Web applications and APIs
Identity and authentication systems
Privileged access management controls
External attack surfaces and exposed services
Most organizations should perform penetration testing at least once per year. Additional testing is recommended when:
New applications or systems are deployed
Cloud infrastructure changes
Major software updates occur
Regulatory or compliance requirements demand it
Professional offensive security testing is carefully planned and executed to minimize disruption. Testing is performed within agreed scopes, timelines, and safety controls to ensure business systems remain stable.
After the assessment, organizations receive a detailed report that includes:
Identified vulnerabilities and attack paths
Risk severity and potential impact
Proof-of-concept exploitation results
Prioritized remediation recommendations
This helps organizations fix weaknesses and improve their security posture.

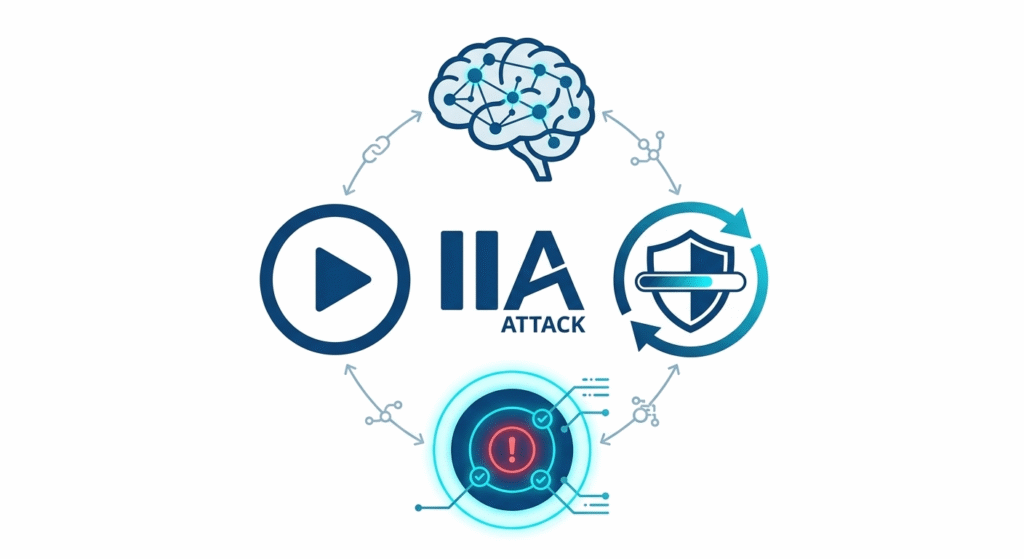
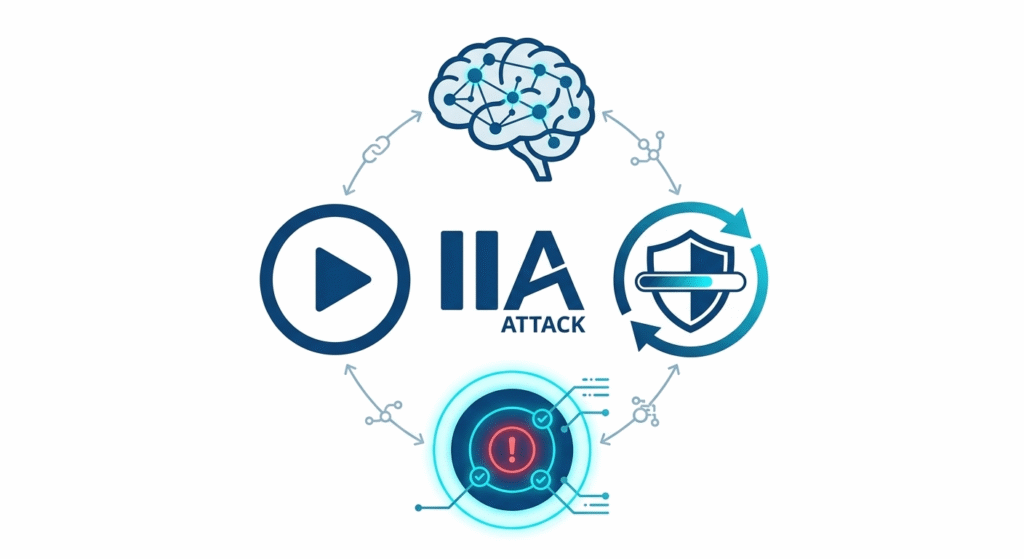
AI-Native 24/7 SOC
AI embedded across detection, response & automation

Outcome-Driven Security
Focused on risk reduction, not just alerts

Continuous Validation
Always tested. Always improving security posture
Cloud & Zero Trust Native
Built for modern cloud-first enterprises
Rapid Deployment
Operational security in weeks, not months
Vendor-Neutral Approach
Unbiased, business-aligned security architecture