Cybersecurity Architecture & Zero Trust Advisory Services
Build a secure foundation for your enterprise with Innovez Cyber’s Cybersecurity Architecture and Zero Trust Advisory Services.
Design resilient, secure, and future-ready environments aligned with modern security principles and business needs.

Overview
Modern enterprises operate in highly distributed environments spanning cloud platforms, SaaS applications, remote workforces, APIs, and hybrid infrastructure. Traditional perimeter-based security models are no longer sufficient to protect against today’s sophisticated cyber threats.
Organizations require a well-designed cybersecurity architecture aligned with business objectives, modern threat landscapes, and Zero Trust principles to ensure secure operations, controlled access, and resilience against cyberattacks.
Innovez Cyber provides comprehensive Cybersecurity Architecture and Zero Trust Advisory Services designed to help organizations assess, design, implement, and continuously improve secure enterprise environments.
Our expert-led services focus on building resilient, scalable, and future-ready security architectures that protect identities, applications, data, cloud environments, and infrastructure while enabling business agility and digital transformation.
Our Approach: Security Architecture Aligned with Modern Enterprise and Zero Trust Principles
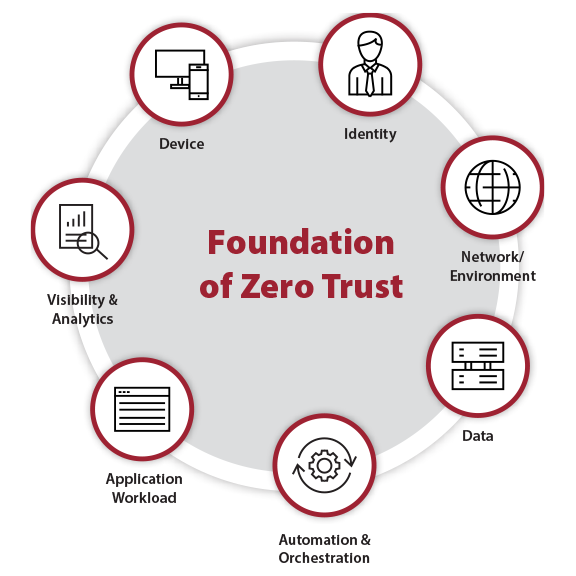
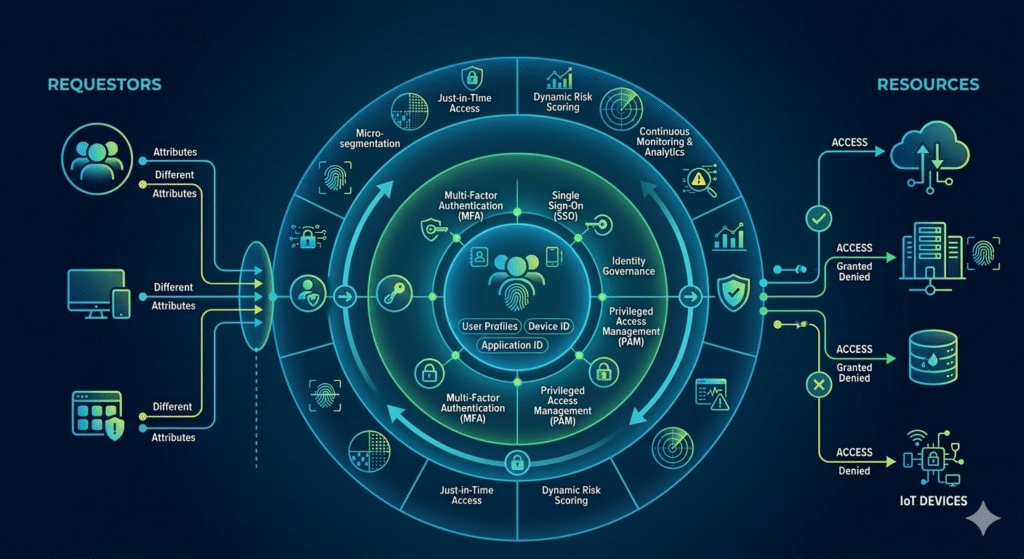
Innovez Cyber follows a structured, service-driven approach to cybersecurity architecture and Zero Trust implementation based on key principles:
- Identity-centric security design
- Least privilege access enforcement
- Continuous verification and risk assessment
- Secure access regardless of location or network
- Layered defense and attack surface reduction
- Secure cloud and hybrid architecture design
- Continuous monitoring and security posture improvement
Our approach ensures that security is integrated into the foundation of enterprise architecture rather than added as an afterthought.

Core Cybersecurity Architecture Services

Security Architecture Assessment and Gap Analysis
Innovez Cyber evaluates your existing cybersecurity architecture to identify risks, weaknesses, and improvement opportunities.
Our services include:
- Assessment of current security architecture and controls
- Identification of security gaps and exposure risks
- Review of identity, access, and network security architecture
- Evaluation of cloud and hybrid security architecture
- Risk analysis aligned with modern threat models
- Recommendations for strengthening architecture and security posture
This helps organizations understand their current security maturity and define improvement priorities.
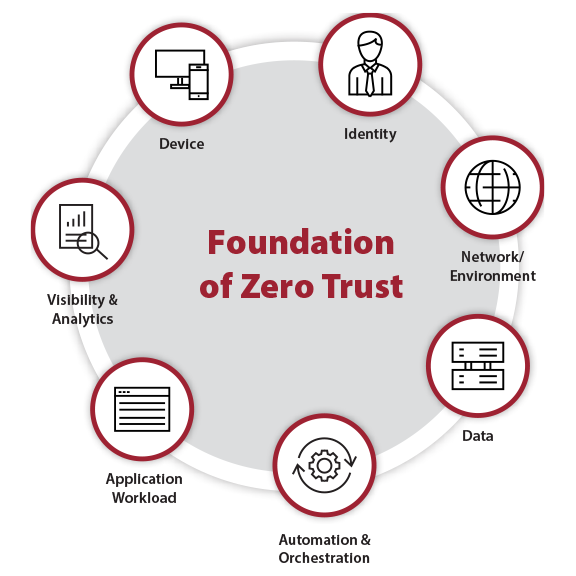
Zero Trust Architecture Strategy and Design
Innovez Cyber helps organizations design and implement Zero Trust security architecture aligned with modern enterprise environments.
Our services include:
- Zero Trust readiness assessment
- Zero Trust strategy development and roadmap design
- Identity-centric access architecture design
- Access segmentation and least privilege implementation advisory
- Continuous access validation and risk-based access guidance
- Secure access architecture across cloud, hybrid, and remote environments
This helps organizations transition from traditional perimeter security to modern Zero Trust security.
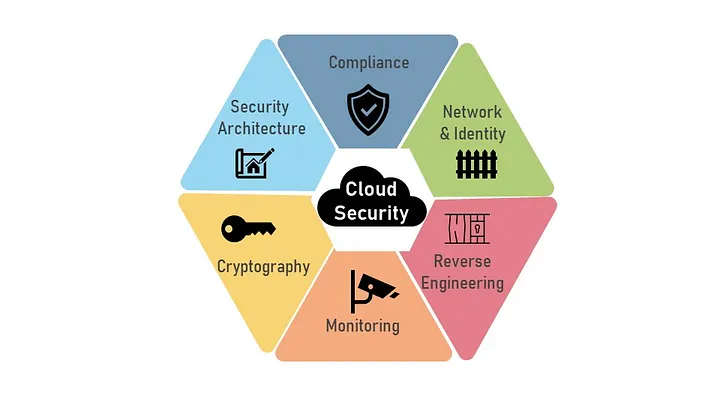
Cloud Security Architecture Advisory
Innovez Cyber provides expert advisory services to design secure cloud architectures aligned with modern security requirements.
Our services include:
- Secure cloud architecture design and assessment
- Identity and access architecture review for cloud environments
- Secure workload and application architecture guidance
- Network segmentation and access control advisory
- Secure cloud deployment and configuration guidance
- Multi-cloud security architecture advisory
This ensures cloud environments are secure, resilient, and properly governed.
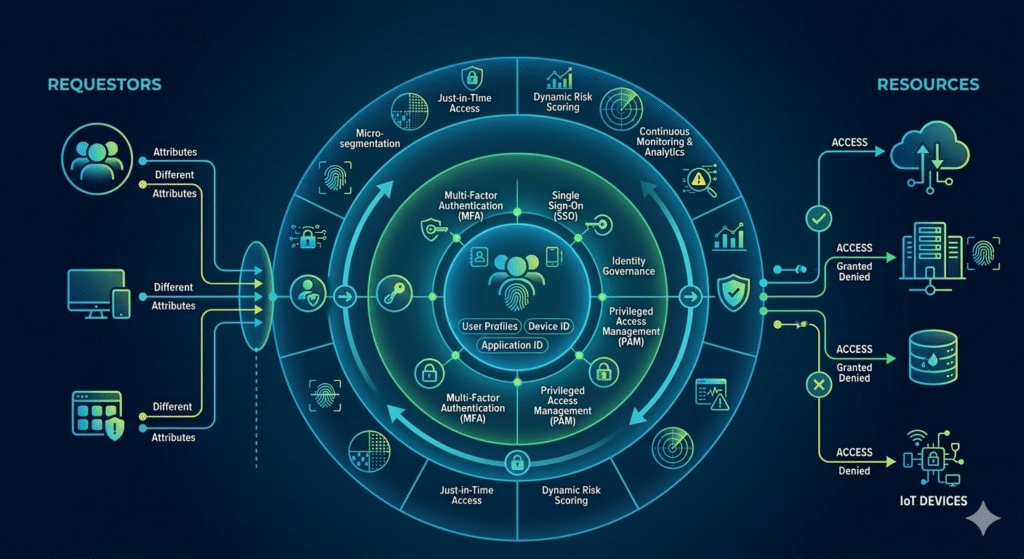
Identity-Centric Security Architecture Design
Identity is the primary control plane for modern security. Innovez Cyber helps design identity-centric security architectures aligned with Zero Trust.
Our services include:
- Identity and access architecture assessment
- Privileged access architecture design advisory
- Access governance and identity control recommendations
- Secure authentication architecture guidance
- Identity risk monitoring and protection advisory
This helps ensure access to critical systems remains secure and controlled.
Network and Access Security Architecture Advisory
Innovez Cyber helps organizations design secure network and access architectures aligned with modern security models.
Our services include:
- Network segmentation and isolation advisory
- Secure remote access architecture guidance
- Secure connectivity and communication design
- Access control architecture recommendations
- Secure hybrid network architecture advisory
This reduces attack surface and prevents unauthorized lateral movement.

Secure Application and Infrastructure Architecture Advisory
Innovez Cyber provides expert guidance to design secure application and infrastructure architectures.
Our services include:
- Secure application architecture design advisory
- Secure infrastructure architecture assessment
- Protection of critical business systems and workloads
- Access control and communication security advisory
- Secure deployment architecture recommendations
This ensures applications and infrastructure are designed with security as a core principle.

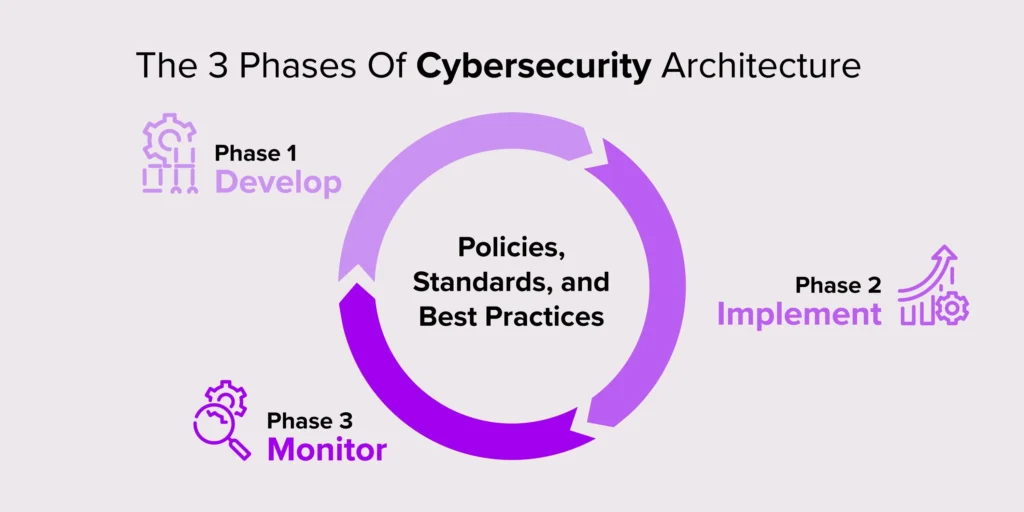
Security Architecture Roadmap and Transformation Planning
Innovez Cyber helps organizations define and implement structured security transformation roadmaps.
Our services include:
- Cybersecurity architecture roadmap development
- Security maturity assessment and improvement planning
- Zero Trust implementation roadmap design
- Prioritized security improvement recommendations
- Long-term security architecture planning
This provides a clear path toward a modern, secure enterprise architecture.

Continuous Architecture Review and Security Advisory
Security architecture must evolve with changing threats and business environments. Innovez Cyber provides ongoing advisory services to ensure architecture remains secure.
Our services include:
- Continuous security architecture review
- Risk and exposure analysis
- Architecture improvement recommendations
- Security posture improvement advisory
- Ongoing Zero Trust maturity enhancement
This ensures long-term security resilience.

Key Benefits
Continuous 24×7 Protection
Round-the-clock monitoring ensures threats are detected and addressed at any time.
Faster Threat Detection and Response
AI-driven analytics and expert analysts reduce detection and response times significantly.
Reduced Risk of Breaches and Business Disruption
Early detection and containment prevent major incidents and operational downtime.
Improved Security Visibility
Gain complete visibility across your cloud, endpoints, identities, and infrastructure.
Access to Enterprise-Grade Security Expertise
Leverage highly skilled cybersecurity professionals without building an in-house SOC.
Scalable and Cost-Effective Security Operations
Flexible service models that scale with your business growth.
What Innovez Cyber Helps Secure
Our cybersecurity architecture and advisory services help protect:

Cloud and hybrid infrastructure
Enterprise networks and connectivity

Applications and digital services

Identity and access systems

Sensitive business and customer data

Remote and distributed workforce environments
Why Innovez Cyber Cybersecurity Architecture & Zero Trust Advisory Services
Innovez Cyber delivers expert-led cybersecurity architecture and Zero Trust advisory services aligned with modern enterprise environments.
Our differentiators include:
- Expert cybersecurity architecture and Zero Trust advisory
- Cloud-native and hybrid architecture expertise
- Identity-centric security architecture approach
- Continuous advisory and security improvement services
- Vendor-neutral and service-centric approach
- Scalable and tailored architecture solutions
Ideal for Organizations That Require
- Cybersecurity architecture assessment and improvement
- Zero Trust architecture design and implementation support
- Secure cloud and hybrid environment architecture
- Security transformation and modernization
- Continuous security architecture advisory
- Enterprise-grade security architecture planning
Threats and Risks We Help Mitigate
Key Benefits
Innovez Cyber helps organizations reduce risks such as:
- Unauthorized access and identity compromise
- Privilege escalation and lateral movement
- Cloud and infrastructure security exposure
- Weak access control and excessive permissions
- Architecture weaknesses and security gaps
- Data breaches and unauthorized access
Our cybersecurity architecture and advisory services help protect:
- Cloud and hybrid infrastructure
- Enterprise networks and connectivity
- Applications and digital services
- Identity and access systems
- Sensitive business and customer data
- Remote and distributed workforce environments
Our USP

AI-Native 24/7 SOC
AI embedded across detection, response & automation

Outcome-Driven Security
Focused on risk reduction, not just alerts

Continuous Validation
Always tested. Always improving security posture
Cloud & Zero Trust Native
Built for modern cloud-first enterprises
Rapid Deployment
Operational security in weeks, not months
Vendor-Neutral Approach
Unbiased, business-aligned security architecture
Common Queries You might have
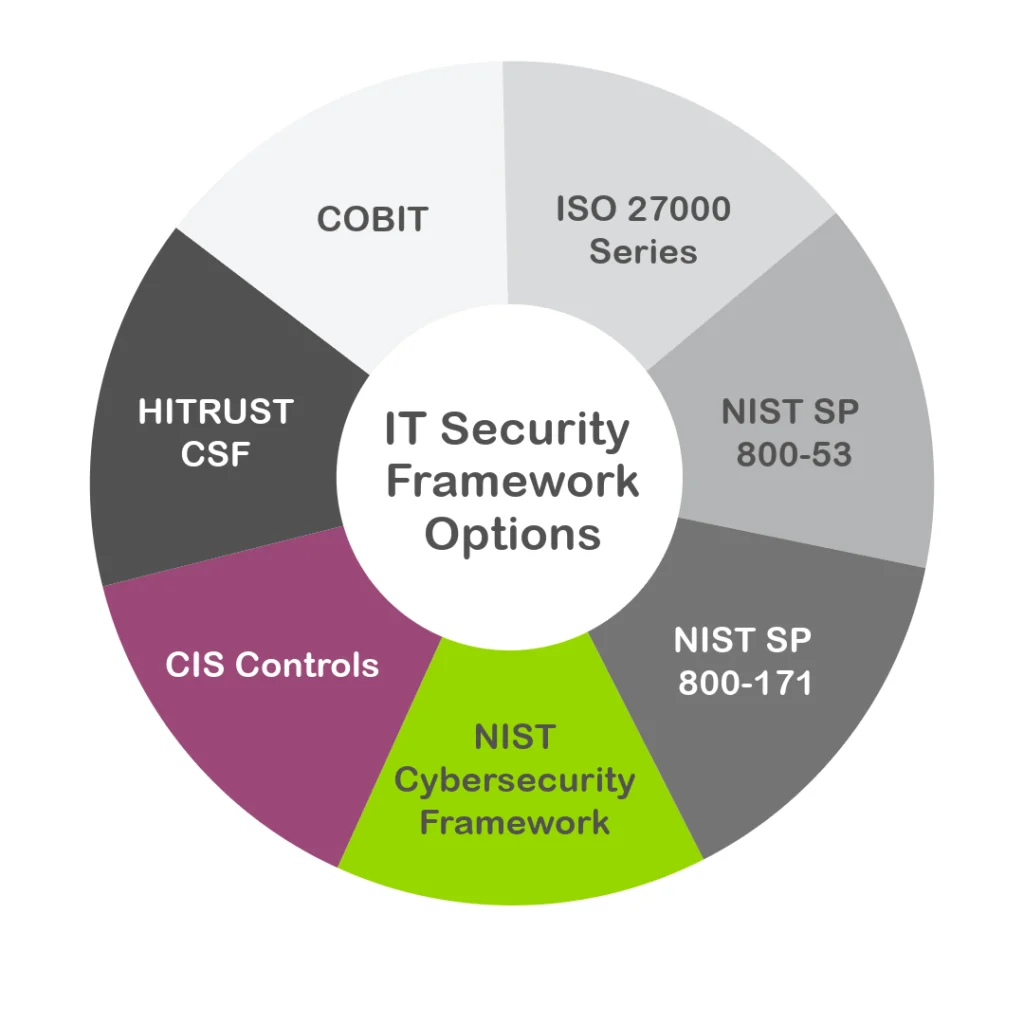
Cybersecurity architecture refers to the design and structure of security controls, technologies, policies, and processes used to protect an organization’s systems, data, applications, and infrastructure.
A well-designed architecture ensures security is integrated into the foundation of enterprise IT environments, rather than added as a reactive measure.
Zero Trust Architecture is a modern security model based on the principle “never trust, always verify.”
Instead of assuming users or devices inside the network are safe, Zero Trust continuously verifies identity, device posture, and access permissions before granting access to resources.
Traditional perimeter-based security models are no longer effective due to:
Cloud adoption
Remote workforces
SaaS applications
Distributed infrastructure
Increasingly sophisticated cyber threats
Modern cybersecurity architecture helps organizations secure cloud, hybrid, and distributed environments effectively.
We help organizations transition to Zero Trust through:
Zero Trust readiness assessments
Architecture strategy development
Identity-centric access control design
Network segmentation recommendations
Continuous verification and monitoring strategies
Our approach aligns with guidance from the National Institute of Standards and Technology (NIST).